The Deep Web

The seamy side of the internet that you dare not explore
In bluish-white letters on a grey background, he claims that he can 'get someone known as a user of child porn, ruin someone financially or get them arrested' for a fee of around €500. He also takes up 'smaller' jobs such as hacking into email or Facebook accounts for just around €200. A chill runs through me as I stare at this, because the claims of this nameless and faceless individual on the other side of a terminal somewhere in the world leave little to my imagination.
For long, the Deep Web has held the attention of the faithful for the darkest of reasons. But in spite of the negative connotations associated with that term, it essentially just refers to that part of cyberspace that is 'off the map' as it were: the part that has not been indexed by standard search engines such as Google, Yahoo! or Bing. By popular estimates, it may well be 500 times the size in gigabyte terms than the usual World Wide Web as search engines know it. It hides in plain sight, catering to patrons across class, creed, sex and language barriers. It promises fulfillment of even the most esoteric and wild fantasies without forcing one to give up the charade of one's offline life. Its reach and penetration is a big question even among the best hackers and cyber security mavens.
This hacker-for-hire that I have on my screen says that he is 'not a pussy and will do anything for money'. He also claims 16 years of experience in the field. To back this up, he substantiates his resume-website with his technical skills: 'HTML, PHP, SQL, APACHE, C, C++, Assembler, Delphi, highly personalized Trojans, Bots, DDOS and spear phishing attacks.' Last but not least, he says he is 'not from some crappy Eastern Europe country' and that he is fluent in English and German. Somewhere, I get the feeling that he is trying too hard.
Whether that would-be mercenary is authentic or fake, it is unlikely that he will ever be caught. This is because the biggest asset he has is also a necessity for Deep Web survival—that of anonymity. For instance, my Internet Protocol (IP) address currently appears to be 37.252.125.188, which corresponds to a location in the Netherlands, but of course, at the click of a button I could easily be in Australia, France or the US.
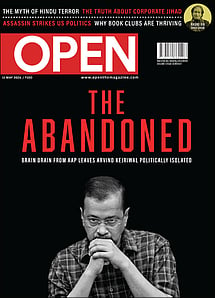
The Abandoned Kejriwal
01 May 2026 - Vol 04 | Issue 69
Brain drain from AAP leaves Arvind Kejriwal politically isolated
ACCESS TO ANONYMITY: THE ONION ROUTER
The first thing I notice about The Onion Router (TOR) is that it makes web surfing annoyingly slow. Simply opening Google Mail, which happens almost instantly on my regular browser, Chrome, takes over 10 seconds on the TOR browser bundle. Nor can I watch videos (of course, there are ways to make that happen, but it has been blocked for a reason). This is the price I will have to pay for more privacy and security in cyberspace.
The Onion Router, originally funded by the US Navy, is maintained by the US-based not-for-profit Tor Project. TOR browser bundle basically comprises Mozilla Firefox version 17 compounded with additional security. When connecting to a site, it shrouds the data from the original computer in multiple layers of encryption (like an onion), which it then routes through a randomly selected network of volunteer computers across the world. At each relay node, a layer is peeled off the onion—decrypted, that is—to get the address of the next relay. The final node in the chain decrypts the last layer to find the destination and transfer the data, without ever finding out its origin or the path it took to get there.
Although TOR does a good job of enabling online anonymity, it is not perfect. This was demonstrated by a hacker group called Anonymous back in 2011 when it launched an attack (called Operation Darknet) on a group of child pornography websites on TOR. The group, working in conjunction with FBI, claimed access to a list of IP addresses of users who frequented those websites. Although Anonymous' method of attack, the Distributed Denial-of-Service or DDoS, did not explicitly point to a chink in TOR's armour, as was also evident from the fact that the websites resumed operations soon after, it did raise enough questions for people to wonder whether the FBI, and by extension the US government, was getting around to breaking TOR.
Last month, the FBI arrested Eric Eoin Marques, who the agency claims as the biggest facilitator of child porn on the planet, shutting down almost all major websites on his online hosting facility on TOR, Freedom Hosting. Over the years, the bi-directional blindness that TOR facilitates has spawned online markets for drugs, arms, pornography, contract killings, forgeries, hacking services, classified information and cyber activism across cyberspace. And this is by no means an exhaustive list.
'HIGH AS A KITE'
The owner of The Silk Road (TSR), a multi-million dollar online enterprise famous for drugs, is a hacker and wannabe philosopher who likes to call himself Dread Pirate Roberts. He greets me with some elder-brotherly advice on my first visit to TSR. He says he knows how I can't wait 'to get to the good stuff', but that I should read his entire letter for my own good. He then tells me to behave myself and refrain from 'child pornography, stolen goods, assassinations and stolen personal information'. He advises me not to scam others or get scammed in return. He preaches some more and says that 'just because you can, doesn't mean you should'. Then it occurs to him that he is not my daddy and that it's for me to judge what's good and what's bad for me. Finally, he signs off as my 'faithful servant'.
For a hidden site that is known as the Mecca of drugs, TSR is remarkably easy to locate. Go ahead. Google it. You'll see. The web addresses to these hidden sites are some random alphanumeric combinations followed by '.onion'. They look as if a cat was let loose on the keyboard when the sites were being named.
Once within the market, I begin to realise why TSR has been making waves. I may not be drooling, but my mouth is wide open and my fingers are frozen because I am literally spoilt for choice. MDMA, ketamine, hash, kush (in pineapple flavour too, if you so desire), crystal meth, DMT, GHB, LSD and scores of other chemical combinations. There are also Penis Envy Shrooms ('Extremely Potent') and ChillPill Capsules with interesting illustrations next to them, though I am not sure what these might be. They are broadly clubbed under 11 groups: Cannabis, Dissociatives, Ecstasy, Intoxicants, Opioids, Others, Precursors, Prescription, Psychedelics, Stimulants and Tobacco. Ironically, a small box to the right of my screen also has links saying, 'Winning the war on drugs' or 'Ask a drug expert physician about drugs and health.'
These drugs are shipped to desirous souls in the US, UK, Netherlands, Germany, Sweden and Australia mostly. And these are priced at anything up to a few million bitcoins (more on this later), although I think anything priced above a few hundred bitcoins may quite possibly be a scam because bitcoins are an expensive currency. Nobody in his right mind would pay that kind of money just for a bunch of pills.
Although TSR has become synonymous with drugs, that is not the only merchandise available. Gold bars, dollar bills, bank accounts, driver's licences, birth/death certificates, passports, explosives, gemstones, Rolexes, Swarovskis, cameras, laptops and what have you. TSR's roaring success has given rise to competition. Soon enough, I am browsing through Atlantis and Black Market Reloaded, the new kids on the block that are bringing the fight out in the open. I stumble upon a YouTube video-cum-advertisement showing how 'Charlie', who was sorely disappointed when he couldn't find dope in his neighbourhood, gets 'high as a kite' after using Atlantis' services. Atlantis also likes to boast about the rating it got in a recent article in Forbes magazine, which had ordered marijuana from all three sources to test how good the service was; Atlantis was rated 'Impressive' while TSR was rated 'Not ideal', and the package from Black Market Reloaded did not even show up. Such publicity finally convinced Dread Pirate Roberts to loosen up a little and agree to an interview with Forbes last month.
THE BITCOIN RUSH
A bitcoin is exactly what its name says—an online currency of information bits, made of 1s and 0s. To get a sense of how a transaction with this digital currency works, imagine a society with a few people, among them you and I, somewhere on Mars (in cyberspace, we would correspond to computer terminals). We all go about using a nickname and nobody knows anybody's true identity. Standard fiat currency, such as the rupee or dollar, has no value on Mars. What we use instead as a means of exchange and store of value is varying bitcoin units, each of which—like a currency note—has a unique ID given by the issuer that cannot be replicated; any attempted counterfeits are caught out by software.
Now if I have 10 bitcoins and would like to give you six bitcoins for some service, this is how it will proceed. I will write out the details of the transaction on memos—who I am dealing with, how much money I want to transfer, how much change I will be left with, and the transaction fee I will be assigning to the successful facilitator of my transaction ('a bitcoin miner')—and then affix the memos with my nick-signature. Then, I send out one such memo each to everyone in the society, including you, by which you know that I am interested in paying you some bitcoins.
The facilitators of my transaction, the bitcoin miners, validate the transaction by verifying whether I have the money I am spending, whether my signature is genuine, and if you, the entity I am paying, even exist. Anybody in the society willing to take up that job could work as a miner, but few survive since it is such a resource-intensive job. Once the verification is done, there is one rather difficult task that the miners must do. Different miners are required to solve variations of a tough puzzle ('proof of work') that indicates that they have authentically done their part of the job and that their work can be trusted. Mind you, the miners are racing each other all this while. The first one to come up with an appropriate proof-of-work will be assigned the responsibility of recording the transaction in an online ledger, the details of which are known to the whole society.
But why do all of this? For the simple reason that everybody likes to get rich. Not only does the successful miner get a transaction fee, he also ends up generating a pre-decided amount of bitcoins (out of thin Martian air, as it were) for himself. Once the puzzle has been solved, the victorious miner sends memos to all other individuals in the society letting them know of his success. The others drop their hard work and start using the updated ledger without whining (yes, in this fictional world of ours, nobody is jealous of anybody).
The above, of course, is an oversimplified view of how bitcoins operate. All these activities happen in cyberspace with the help of cryptographic functions and complex calculations with a host of inbuilt mechanisms to detect and prevent fraud. An interesting aspect of the above transaction is that although the entire society is aware of the financial details, nobody knows the true identities of the two parties since everyone in this society is represented by a series of numbers—like with 'numbered' Swiss bank accounts of old—or nicknames.
The main reason for coining the bitcoin, as its founder Satoshi Nakamoto pointed out, was to rid currency management of human subjectivity—as exercised by central banks—and let the reliability of mathematical formulae rule the currency. As Nakamoto wrote on his blog, the trust invested in financial institutions and the breach of that trust was the cause of most troubles with fiat currency. It is telling that the true identity of Satoshi Nakamoto has never been found.
The bitcoin can at best be considered an experiment, but it is one that is gaining acceptance rapidly. Bitcoin banks, exchanges (such as the famous MT. Gox in Tokyo) and even trading counters have arisen across different continents. Although it is highly volatile (its value in US dollars at Mt Gox has gone from 90 to 140 over the past two months), people are putting more and more faith in it because non-sentimental mathematics has historically proven to be a better friend than greedy bankers.
THE ENDLESS ICEBERG
One of the analogies that people favour to describe the Deep Web is that of an iceberg, and nine-tenths of an iceberg cannot be seen. The Deep Web does one better. The bottom of an iceberg can be scraped if you dive reasonably deep, but the depths of the Deep Web can only be left to your imagination. For those who must take a dive, there is the Hidden Wiki to your rescue (How could there not be?).
After I enter the cat-pawed web-address, I land up at an almost blank page with an onion saying 'Hello' on the title bar and a single statement at the top left asking me, 'Looking for the Hidden Wiki?' Of course, you moron. The Hidden Wiki, though not as fancy as your usual Wiki, is pretty handy as an entry point to the Deep Web. In neatly listed bullet points, it offers me TOR addresses to each of the activities I have mentioned so far, and more. I start clicking on random links one after the other, and realise with a pang of disappointment that many don't work. But the ones that do, lead me to another thousand links. It would be pointless to write on everything that catches my attention—and rest assured, the Deep Web is an extremely intriguing place—and even if I did, you wouldn't be satisfied.
I have been exploring this hidden world for five nights now and I have had enough. The honeymoon, as they say, is over. Unless you are a criminal, a sexual deviant, dope-fiend, activist, whistleblower or just an incorrigible anarchist, chances are that you will want out. Frankly, the usage and speed constraints are too much for a 'normal' user to handle. Me, I am just a curious journalist, and for now, I am not sure I need a bulletproof vest.